Notizie per Categorie
Articoli Recenti
- Microsoft helps media customers capitalize on AI for greater ROI 2 Aprile 2025
- [In preview] Public Preview: Multi-cluster Eviction and Disruption Budgets with Azure Kubernetes Fleet Manager 2 Aprile 2025
- Microsoft Adaptive Cloud: Advancing edge computing in the defense sector 2 Aprile 2025
- [Launched] Generally Available: Network isolated cluster in AKS 2 Aprile 2025
- [In preview] Public Preview: Multiple Load Balancers for AKS 2 Aprile 2025
- [In preview] Public Preview: Service Allowed IP Ranges in AKS 2 Aprile 2025
- [Launched] Generally Available: Cilium Endpoint Slices in AKS 2 Aprile 2025
- [In preview] Public Preview: Advanced Container Networking Services Cilium L7 Policies Support in AKS 2 Aprile 2025
- [Launched] Generally Available: Azure CNI Node Subnet + Cilium Support 2 Aprile 2025
- [Launched] Generally Available: AKS Cost Recommendations in Azure Advisor 2 Aprile 2025
Today we’re on the verge of a monumental shift in the technology landscape that will forever change the security community. AI and machine learning may embody the most consequential technology advances of our lifetime, bringing huge opportunities to build, discover, and create a better world. Brad Smith recently[…]
Read More
Today we’re on the verge of a monumental shift in the technology landscape that will forever change the security community. AI and machine learning may embody the most consequential technology advances of our lifetime, bringing huge opportunities to build, discover, and create a better world. Brad Smith recently[…]
Read MoreIn my practice as a Microsoft Global Black Belt, I focus on the technical and business enablement aspects of protecting organizations from cyber threats with tools like Microsoft 365 Defender, Microsoft Purview and Microsoft Sentinel. In my role as a board member for another publicly traded company, the[…]
Read More
Today marks a significant shift in endpoint management and security. We’re launching the Microsoft Intune Suite, which unifies mission-critical advanced endpoint management and security solutions into one simple bundle. The new Intune Suite can simplify our customers’ endpoint management experience, improve their security posture, and keep people at[…]
Read MoreI don’t know about you, but we’re still catching our breath after 2022. Microsoft Security blocked more than 70 billion email and identity threats last year.1 In the same 12-month span, ransomware attacks impacted more than 200 large organizations in the United States alone, spanning government, education, and[…]
Read MoreAdopting Zero Trust security for your enterprise is no longer a wish-list item—it’s a business imperative. The workplace today extends to almost anywhere, anytime, from any device. Siloed, patchwork security solutions leave gaps that threat actors continue to exploit. A comprehensive Zero Trust model provides the integrated security[…]
Read More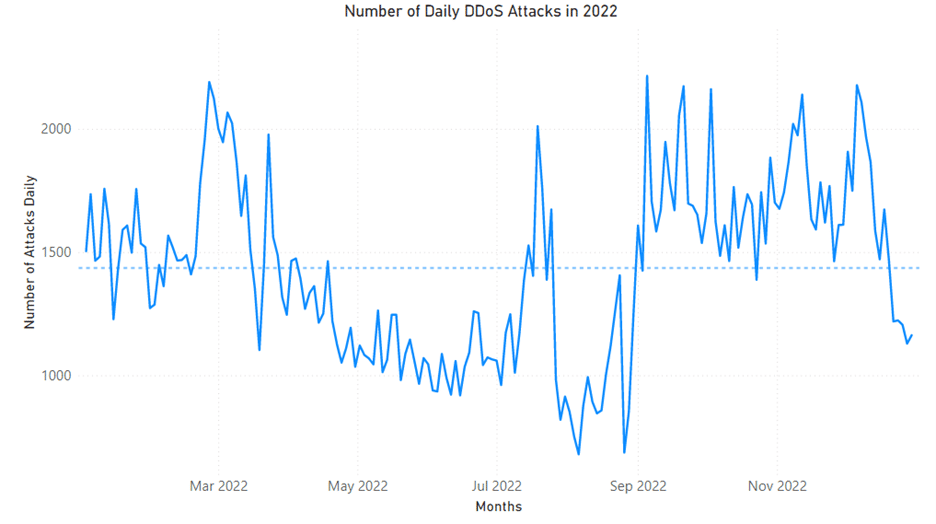
As organizations strengthen their defenses and take a more proactive approach to protection, attackers are adapting their techniques and increasing the sophistication of their operations. Cybercrime continues to rise with the industrialization of the cybercrime economy providing cybercriminals with greater access to tools and infrastructure. In the first[…]
Read More
In today’s world where hybrid and remote work are on the rise, and companies rely on email now more than ever, phishing remains one of the most prominent and sophisticated techniques that malicious actors utilize to attack organizations and gain access to their most sensitive information. Twenty-seven percent[…]
Read More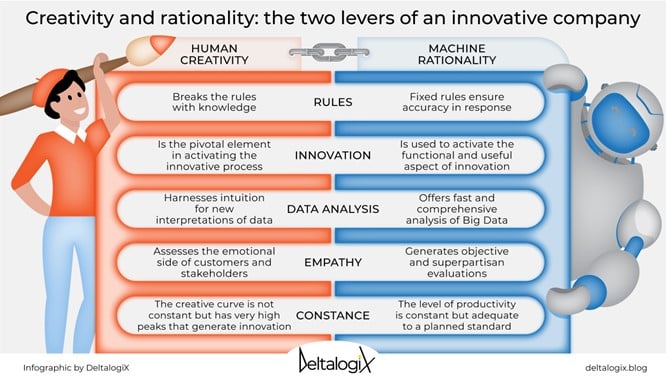
The security community is continuously changing, growing, and learning from each other to better position the world against cyberthreats. In the latest post of our Community Voices blog series, Microsoft Security Senior Product Marketing Manager Brooke Lynn Weenig talks with Linda Grasso, the founder and chief executive officer of DeltalogiX, a blog that provides business leaders with the latest technology news.[…]
Read More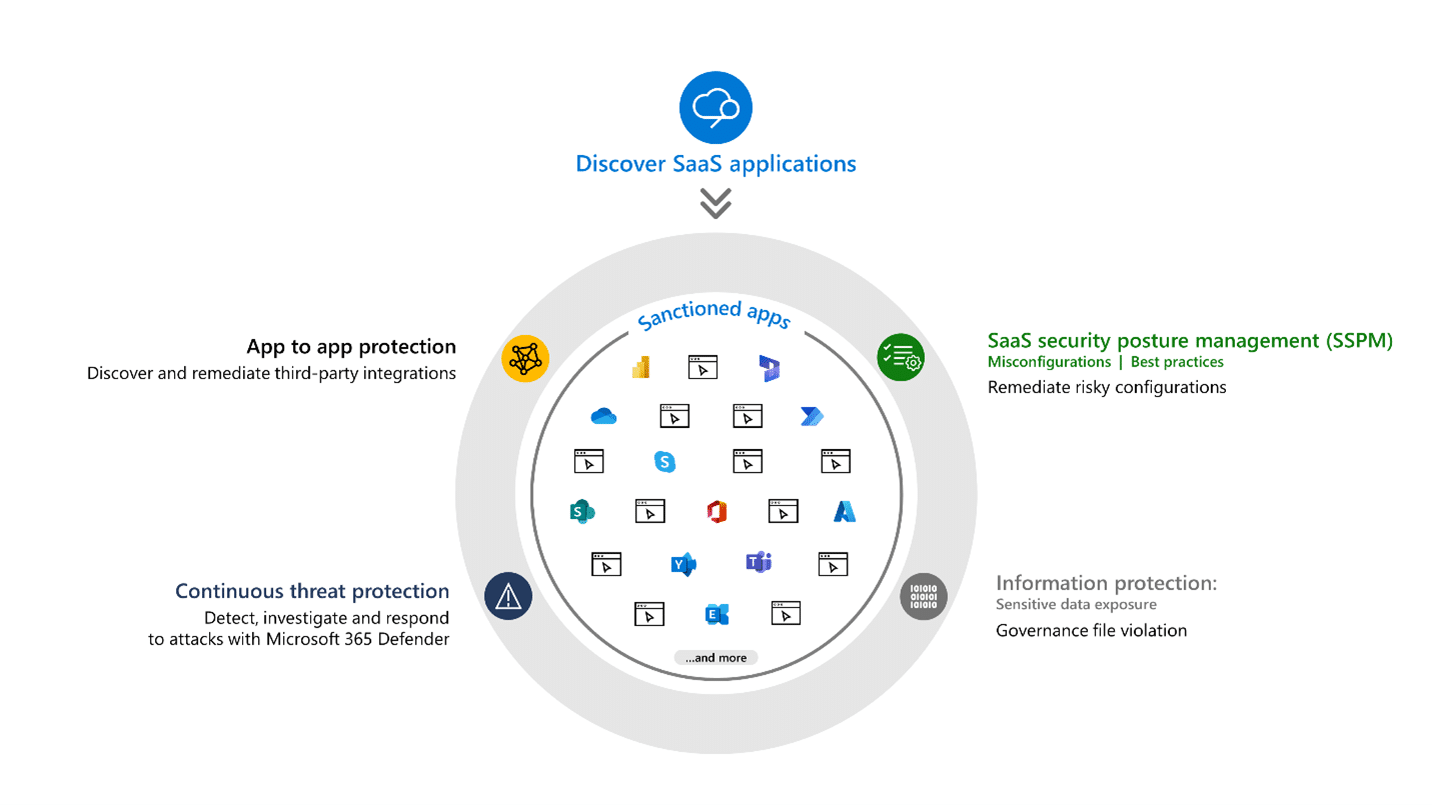
Software as a service (SaaS) apps are ubiquitous, hybrid work is the new normal, and protecting them and the important data they store is a big challenge for organizations. Today, 59 percent of security professionals find the SaaS sprawl challenging to manage1 and have identified cloud misconfigurations as[…]
Read More