Notizie per Categorie
Articoli Recenti
- [In preview] Public Preview: Azure Front Door Premium now supports Azure Private Link origins in UAE North 10 Febbraio 2026
- [In preview] Public Preview: Azure Front Door Premium now supports Azure Private Link origins in UAE North 10 Febbraio 2026
- [Launched] Generally Available: Azure Databricks Supervisor Agent 10 Febbraio 2026
- [Launched] Generally Available: Azure Databricks Supervisor Agent 10 Febbraio 2026
- 80% of Fortune 500 use active AI Agents: Observability, governance, and security shape the new frontier 10 Febbraio 2026
- Manipulating AI memory for profit: The rise of AI Recommendation Poisoning 10 Febbraio 2026
- [In preview] Public Preview: Application Gateway for Containers – AKS managed add-on 9 Febbraio 2026
- [In preview] Public Preview: Application Gateway for Containers – AKS managed add-on 9 Febbraio 2026
- A one-prompt attack that breaks LLM safety alignment 9 Febbraio 2026
- Analysis of active exploitation of SolarWinds Web Help Desk 7 Febbraio 2026
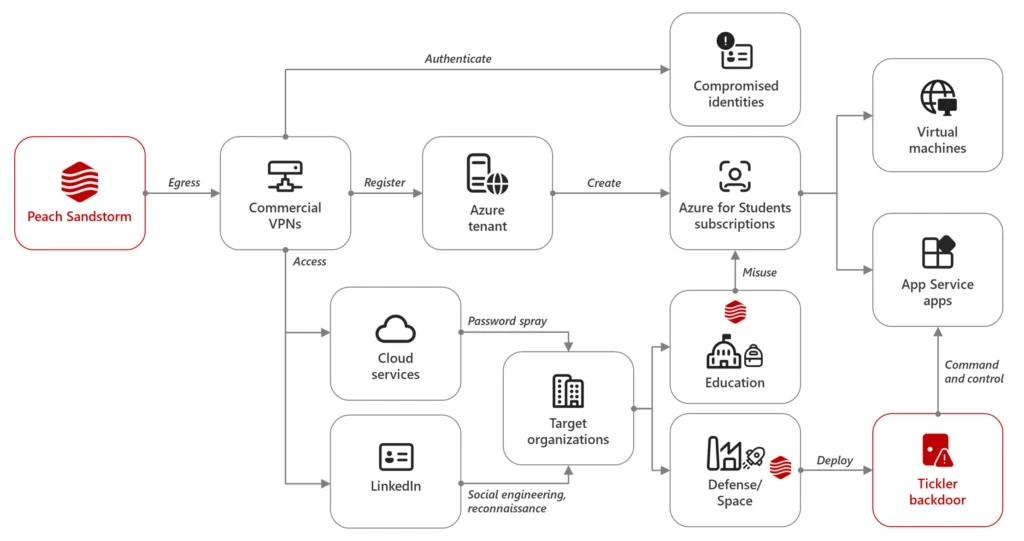
Between April and July 2024, Microsoft observed Iranian state-sponsored threat actor Peach Sandstorm deploying a new custom multi-stage backdoor, which we named Tickler. Tickler has been used in attacks against targets in the satellite, communications equipment, oil and gas, as well as federal and state government sectors in[…]
Read More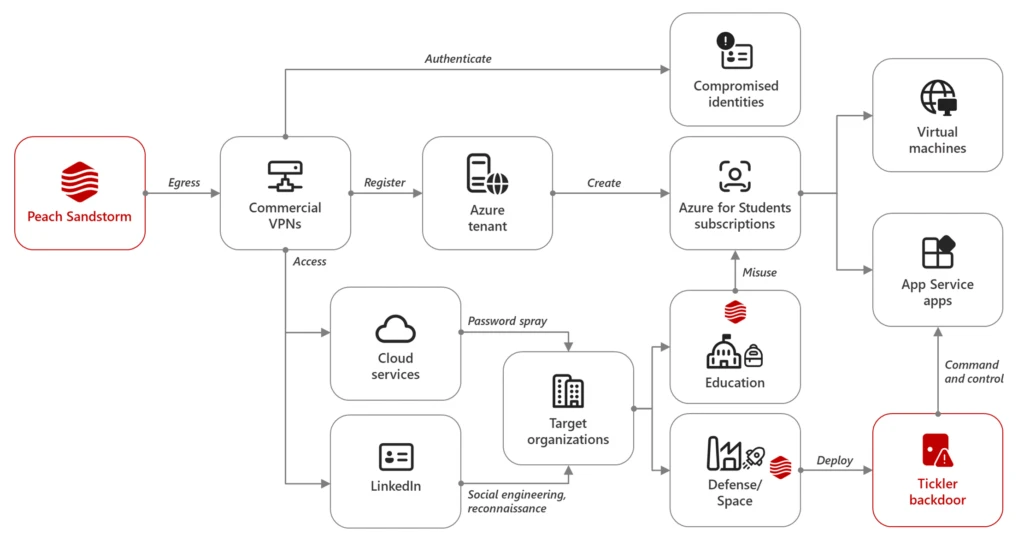
Between April and July 2024, Microsoft observed Iranian state-sponsored threat actor Peach Sandstorm deploying a new custom multi-stage backdoor, which we named Tickler. Tickler has been used in attacks against targets in the satellite, communications equipment, oil and gas, as well as federal and state government sectors in[…]
Read More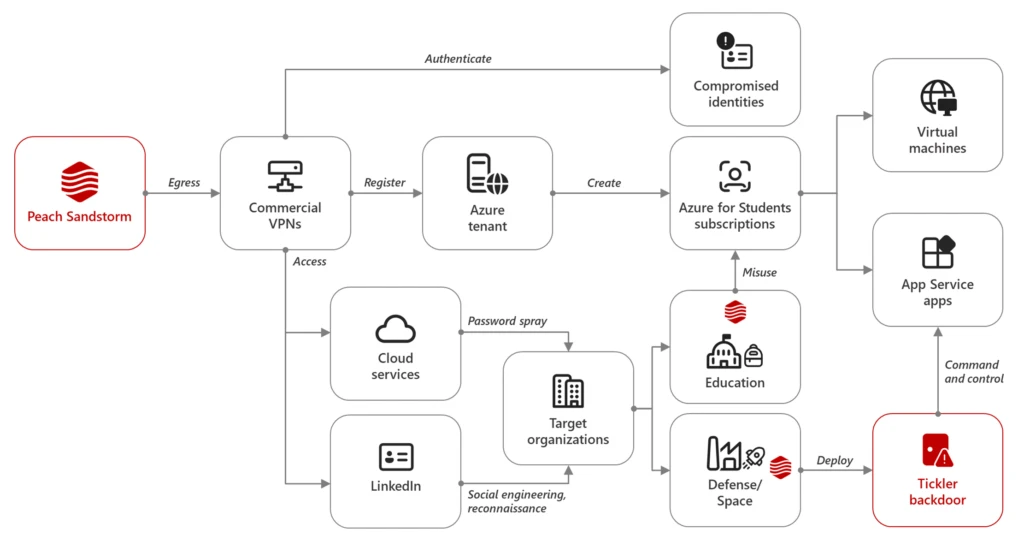
Between April and July 2024, Microsoft observed Iranian state-sponsored threat actor Peach Sandstorm deploying a new custom multi-stage backdoor, which we named Tickler. Tickler has been used in attacks against targets in the satellite, communications equipment, oil and gas, as well as federal and state government sectors in[…]
Read More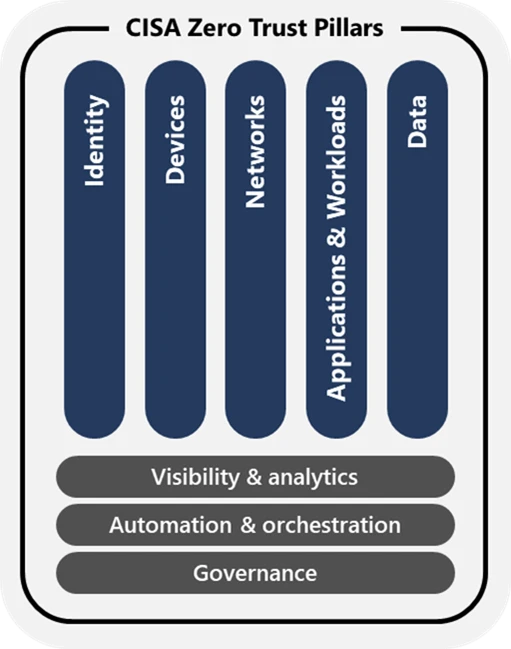
If you’re in charge of cybersecurity for a United States government agency, you’re already familiar with Memorandum M-22-09, “Moving the U.S. Government Toward Zero Trust Cybersecurity Principles,” which the US Office of Management and Budget issued in January 2022. This memo set a September 30, 2024, deadline for[…]
Read More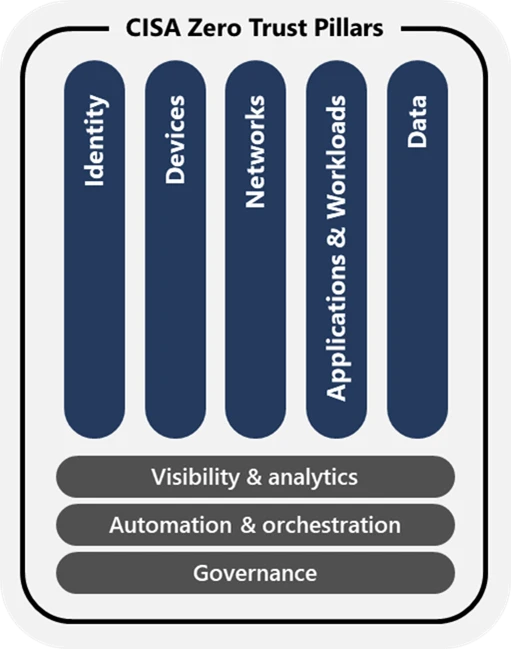
If you’re in charge of cybersecurity for a United States government agency, you’re already familiar with Memorandum M-22-09, “Moving the U.S. Government Toward Zero Trust Cybersecurity Principles,” which the US Office of Management and Budget issued in January 2022. This memo set a September 30, 2024, deadline for[…]
Read More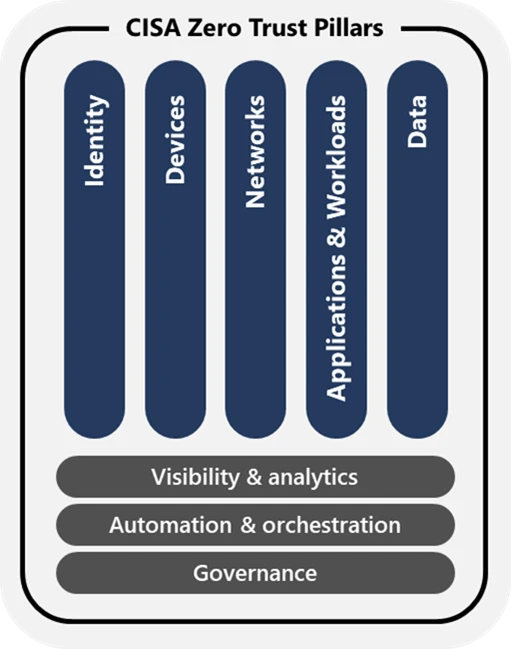
If you’re in charge of cybersecurity for a United States government agency, you’re already familiar with Memorandum M-22-09, “Moving the U.S. Government Toward Zero Trust Cybersecurity Principles,” which the US Office of Management and Budget issued in January 2022. This memo set a September 30, 2024, deadline for[…]
Read More
For the second year, the Microsoft AI Tour will bring together security practitioners, developers, and other technology professionals to learn about the latest AI innovations across the full Microsoft Security stack in multiple cities around the globe. Whether you’re a decision maker who evaluates investments, an IT team[…]
Read More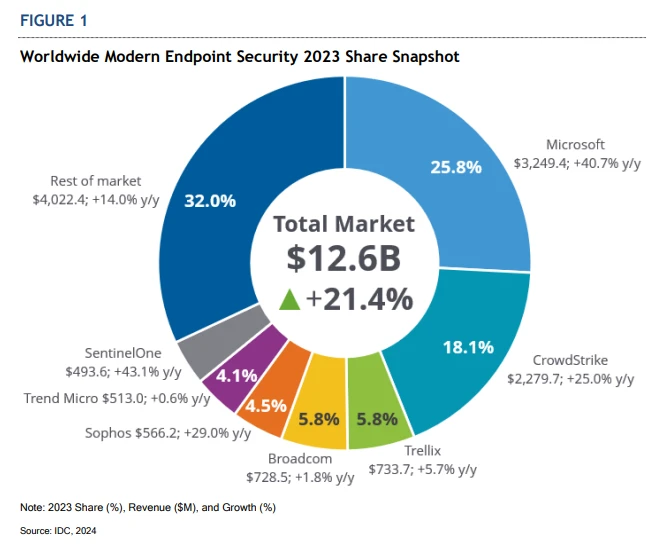
Today’s remote workforce has become the standard. But the security challenges created by remote work continue to be a key point of exploitation by bad actors. In fact, 80% to 90% of all successful ransomware compromises originate through unmanaged devices.1 Because endpoints are a broadly targeted vector and[…]
Read More
Get ready to ignite your passion for innovation at the 2024 Power Platform Community Conference (PPCC). This year, we’re bringing together some of the brightest minds and most enthusiastic members of the Microsoft Power Platform community for an unforgettable experience. Whether you’re a seasoned professional or just starting[…]
Read More
Microsoft researchers recently identified multiple medium severity vulnerabilities in OpenVPN, an open-source project with binaries integrated into routers, firmware, PCs, mobile devices, and many other smart devices worldwide, numbering in the millions. Attackers could chain and remotely exploit some of the discovered vulnerabilities to achieve an attack chain[…]
Read More