Notizie per Categorie
Articoli Recenti
- [Launched] Generally Available: New Microsoft Dev Box Regional Availability 1 Aprile 2025
- [In preview] Public Preview: CNI Overlay for Application Gateway for Containers and AGIC 1 Aprile 2025
- Transforming public sector security operations in the AI era 1 Aprile 2025
- [In preview] Public Preview: Azure Front Door Custom Cipher Suite 1 Aprile 2025
- [Launched] Public Preview: Azure Monitor Application Insights Auto-Instrumentation for Java and Node Microservices on AKS 1 Aprile 2025
- Retirement: Log Analytics Beta API to Be Retired on March 31, 2026 1 Aprile 2025
- Retirement: Log Analytics Batch API to Be Retired on March 31, 2028 1 Aprile 2025
- [In preview] Public Preview: ExpressRoute Resiliency Enhancements 1 Aprile 2025
- Retirement: Azure Machine Learning SDK v1 Will Be Retired on March 31, 2025 – Transition to Machine Learning SDK v2 31 Marzo 2025
- Retirement: Cloud Services (Extended Support) to Be Retired on March 31, 2027 31 Marzo 2025

Microsoft’s cyberphysical system researchers recently identified multiple high-severity vulnerabilities in the CODESYS V3 software development kit (SDK), a software development environment widely used to program and engineer programmable logic controllers (PLCs). Exploitation of the discovered vulnerabilities, which affect all versions of CODESYS V3 prior to version 3.5.19.0, could[…]
Read More
With more than 90 percent of organizations adopting a multicloud strategy1 and cloud-based cyberattacks growing 48 percent year over year,2 securing multicloud and hybrid environments is more important than ever. To successfully protect multicloud infrastructure—where customers are utilizing two or more cloud providers—as well as applications and data,[…]
Read More
With more than 90 percent of organizations adopting a multicloud strategy1 and cloud-based cyberattacks growing 48 percent year over year,2 securing multicloud and hybrid environments is more important than ever. To successfully protect multicloud infrastructure—where customers are utilizing two or more cloud providers—as well as applications and data,[…]
Read More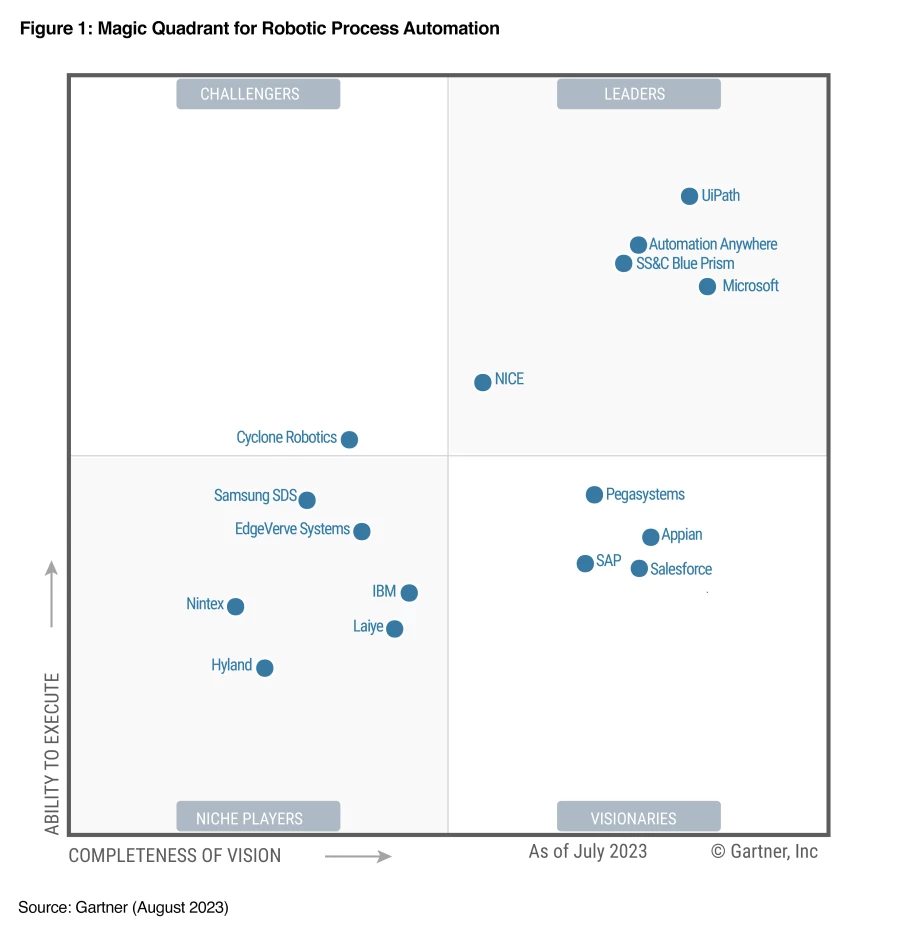
For the third consecutive year, Microsoft has been named a Leader in the Gartner® Magic Quadrant™ for Robotic Process Automation. This year Microsoft is positioned furthest in Completeness of Vision. We would like to thank our millions of active users and community members using Power Automate who helped[…]
Read More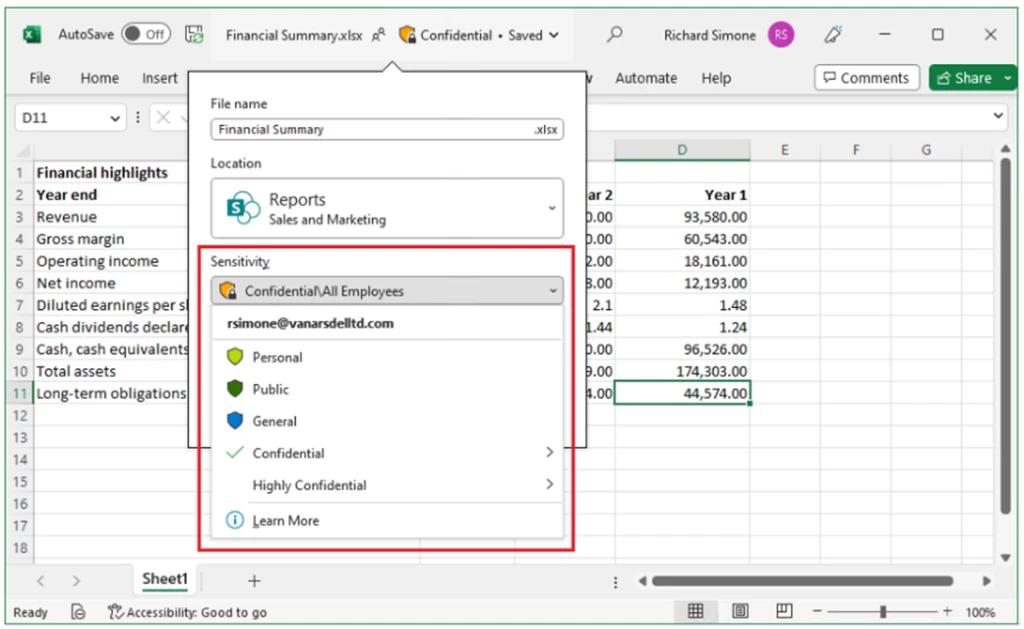
I recently worked with an enterprise customer who experienced a data exfiltration attack using the characteristics of the BazaCall campaign. BazaCall can be both a ransomware and data exfiltration attack that are used together to increase pressure on and damage to the victim. Microsoft Purview has data security[…]
Read More
I recently worked with an enterprise customer who experienced a data exfiltration attack using the characteristics of the BazaCall campaign. BazaCall can be both a ransomware and data exfiltration attack that are used together to increase pressure on and damage to the victim. Microsoft Purview has data security[…]
Read More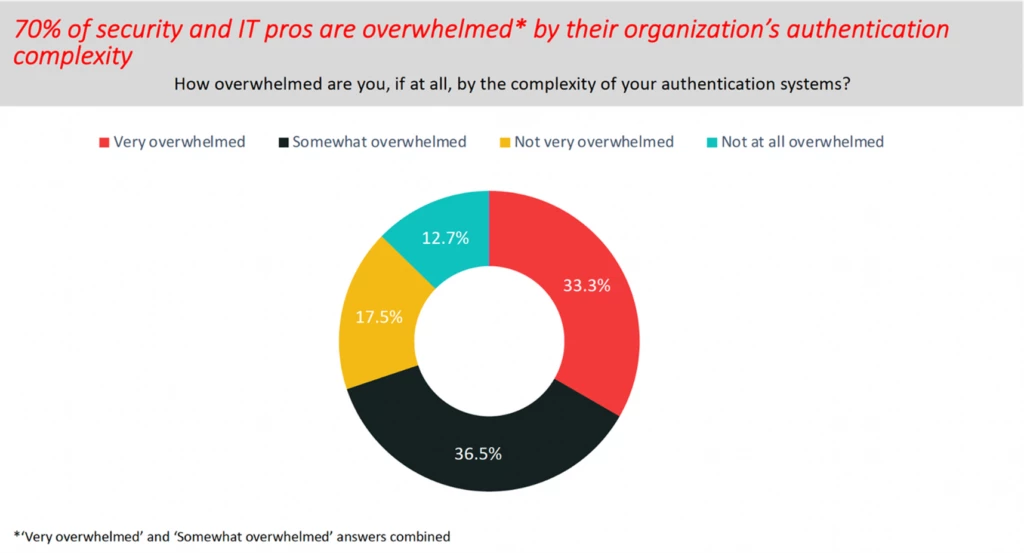
This blog post is part of the Microsoft Intelligent Security Association guest blog series. Learn more about MISA. Passwords are a security weakness and phishing attacks to exploit accounts protected by passwords are on the rise. The last 12 months have seen an average of more than 4,000 password attacks[…]
Read More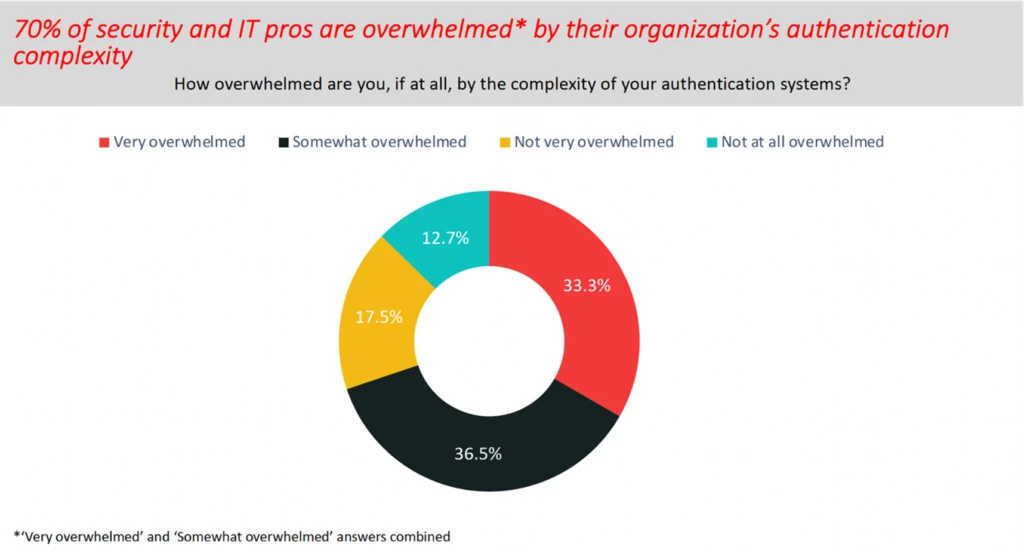
This blog post is part of the Microsoft Intelligent Security Association guest blog series. Learn more about MISA. Passwords are a security weakness and phishing attacks to exploit accounts protected by passwords are on the rise. The last 12 months have seen an average of more than 4,000 password attacks[…]
Read MoreThe recently published United States National Cybersecurity Strategy warns that many popular Internet of Things (IoT) devices are not sufficiently secure to protect against many of today’s common cybersecurity threats.1 The strategy also cautions that many of these IoT devices are difficult—or, in some cases, impossible—to patch or[…]
Read More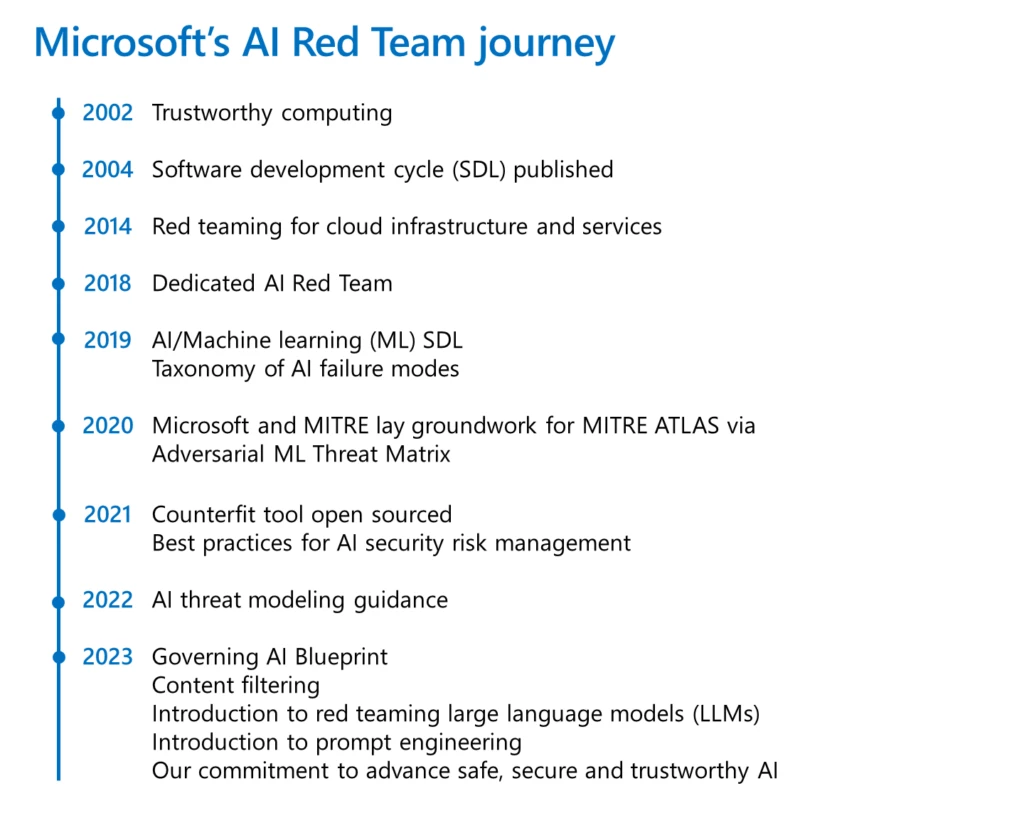
An essential part of shipping software securely is red teaming. It broadly refers to the practice of emulating real-world adversaries and their tools, tactics, and procedures to identify risks, uncover blind spots, validate assumptions, and improve the overall security posture of systems. Microsoft has a rich history of[…]
Read More