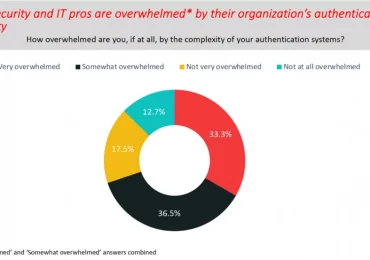
This blog post is part of the Microsoft Intelligent Security Association guest blog series. Learn more about MISA. Passwords are a security[…]
Leggi di piùThe recently published United States National Cybersecurity Strategy warns that many popular Internet of Things (IoT) devices are not sufficiently[…]
Leggi di più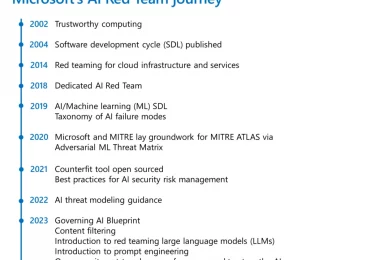
An essential part of shipping software securely is red teaming. It broadly refers to the practice of emulating real-world adversaries[…]
Leggi di più
Today we released the fifth edition of Cyber Signals, spotlighting threats to large venues, and sporting and entertainment events, based[…]
Leggi di più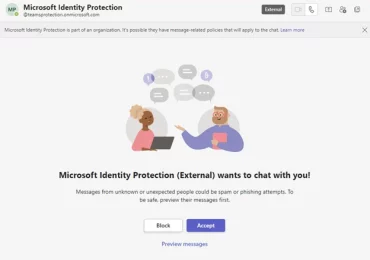
Microsoft Threat Intelligence has identified highly targeted social engineering attacks using credential theft phishing lures sent as Microsoft Teams chats[…]
Leggi di più
In the ever-evolving world of cybersecurity, email remains a primary attack vector for cybercriminals, making effective email protection a foundational[…]
Leggi di più
Now in its twenty-sixth year, Black Hat USA takes place August 5 to 10, 2023, at Mandalay Bay in Las[…]
Leggi di più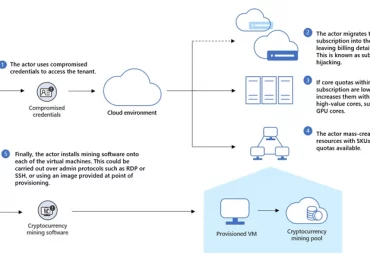
In cloud environments, cryptojacking – a type of cyberattack that uses computing power to mine cryptocurrency – takes the form[…]
Leggi di piùThe security community is continuously changing, growing, and learning from each other to better position the world against cyberthreats. In the latest post of our Community[…]
Leggi di più
Microsoft Power Platform continues to be a leader in the low-code/no-code revolution across the globe, transforming opportunities for individuals and[…]
Leggi di più
As Department of Defense (DoD) Chief Information Officer Hon. John Sherman said recently, Cybersecurity Maturity Model Certification (CMMC) is necessary[…]
Leggi di più
It has been an eventful time since the introduction of Microsoft Security Experts.1 We launched Defender Experts for Hunting, our[…]
Leggi di più