Azure Container Apps dynamic sessions offers serverless, isolated sandboxes for executing untrusted code. The latest update includes support for native JavaScript code execution in public preview. This new JavaScript code interpreter augments the existing Source: Microsoft Azure – aggiornamenti
Read MoreEnd of support for Microsoft Fabric Runtime 1.1 was announced July 12, 2024. We recommend that you upgrade your Fabric workspace and environments to use Runtime 1.3 (Apache Spark 3.5 and Delta Lake 3.2). This latest Fabric Runtime 1.3 also offers a Native Source: Microsoft Azure – aggiornamenti
Read MoreOn March 31, 2025, the Image Analysis 4.0 Preview APIs will be retired. Before that date, you’ll need to migrate your Azure Image Analysis workloads to the Image Analysis 4.0 GA API. We encourage you to make the transition sooner to gain access to improve Source: Microsoft Azure[…]
Read More
AI isn’t just a tool—it’s the foundation for building competitive advantage. In a recent post, we showed how chief marketing officers (CMOs) can move beyond AI experimentation to prove more value and return on their AI investments. To deliver more business impact, CMOs need to expand the way[…]
Read More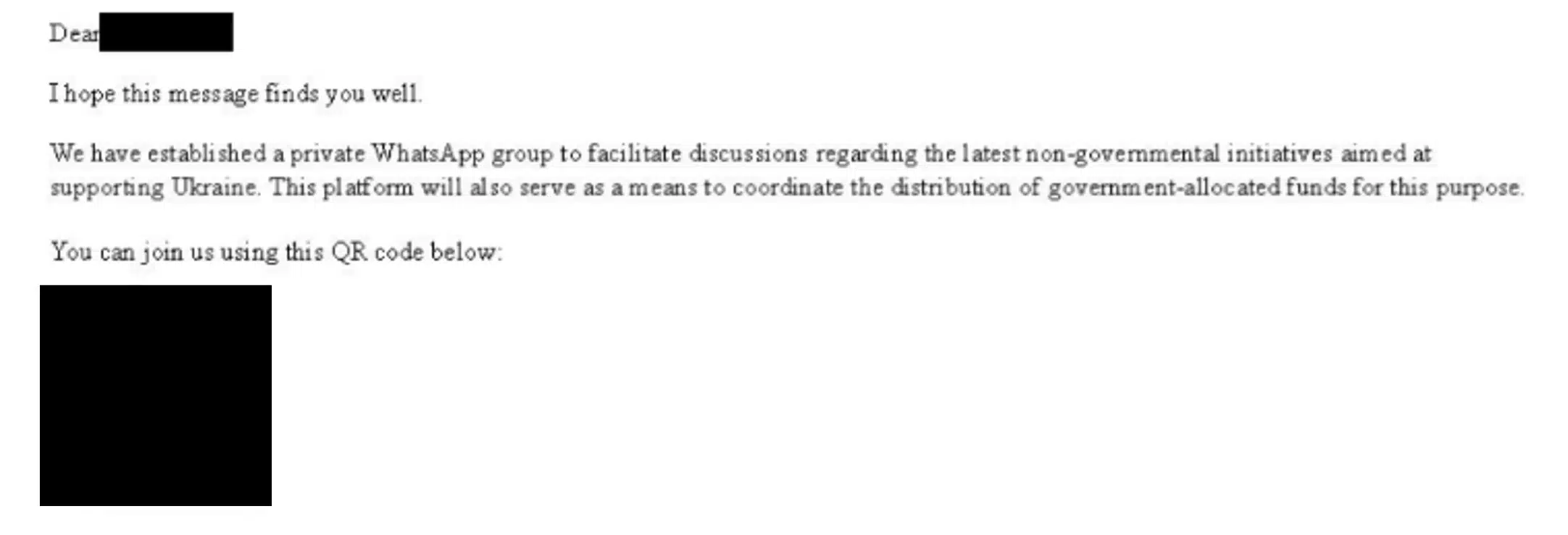
In mid-November 2024, Microsoft Threat Intelligence observed the Russian threat actor we track as Star Blizzard sending their typical targets spear-phishing messages, this time offering the supposed opportunity to join a WhatsApp group. This is the first time we have identified a shift in Star Blizzard’s longstanding tactics,[…]
Read MoreNotizie per Categorie
Articoli Recenti
- Exploitation of CLFS zero-day leads to ransomware activity 8 Aprile 2025
- Meet the Deputy CISOs who help shape Microsoft’s approach to cybersecurity 8 Aprile 2025
- The transformative impact of AI and generative AI on OSS and BSS in telecommunications 8 Aprile 2025
- Tech Accelerator: Azure security and AI adoption 7 Aprile 2025
- Enhancing healthcare productivity and security with Windows Cloud solutions 3 Aprile 2025
- Enhancing healthcare productivity and security with Windows Cloud solutions 3 Aprile 2025
- Enhancing healthcare productivity and security with Windows Cloud solutions 3 Aprile 2025
- Threat actors leverage tax season to deploy tax-themed phishing campaigns 3 Aprile 2025
- Threat actors leverage tax season to deploy tax-themed phishing campaigns 3 Aprile 2025
- Threat actors leverage tax season to deploy tax-themed phishing campaigns 3 Aprile 2025
