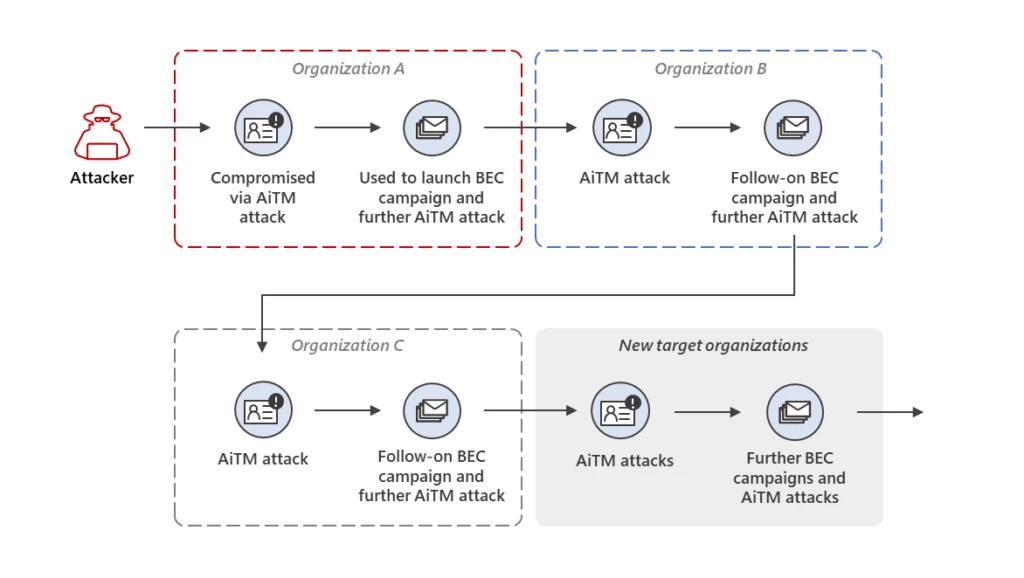
Microsoft Defender Experts uncovered a multi-stage adversary-in-the-middle (AiTM) phishing and business email compromise (BEC) attack against banking and financial services organizations. The attack originated from a compromised trusted vendor and transitioned into a series of AiTM attacks and follow-on BEC activity spanning multiple organizations. This attack shows the[…]
Read MoreYou can now take advantage of unused Azure computing with Azure Container Instances (ACI) Source: Microsoft Azure – aggiornamenti
Read More
In today’s interconnected world, there’s virtually no limit to what technology can help us achieve. Millions of connections happen every moment between people, machines, apps, and devices. Digital connectivity fuels new possibilities for us in business, helps us make positive changes in the way we live and work,[…]
Read More
In the post-COVID-19 environment, providers and other healthcare organizations face complex challenges. They contend with staffing shortages, employee burnout, rising costs, an evolving regulatory environment, new care delivery requirements, and shifting business models. Protecting data security in healthcare is also a pressing concern. In response, providers are increasingly[…]
Read MoreWith this announcement, cloud native and modern applications that use REST APIs to access Azure SMB shares can utilize identity-based authentication and authorization to access file shares. Source: Microsoft Azure – aggiornamenti
Read MoreNotizie per Categorie
Articoli Recenti
- Enhancing healthcare productivity and security with Windows Cloud solutions 3 Aprile 2025
- Enhancing healthcare productivity and security with Windows Cloud solutions 3 Aprile 2025
- Enhancing healthcare productivity and security with Windows Cloud solutions 3 Aprile 2025
- Threat actors leverage tax season to deploy tax-themed phishing campaigns 3 Aprile 2025
- Threat actors leverage tax season to deploy tax-themed phishing campaigns 3 Aprile 2025
- Threat actors leverage tax season to deploy tax-themed phishing campaigns 3 Aprile 2025
- Shaping the future of product engineering and research and development with generative AI 3 Aprile 2025
- Shaping the future of product engineering and research and development with generative AI 3 Aprile 2025
- Shaping the future of product engineering and research and development with generative AI 3 Aprile 2025
- [In preview] Public Preview: Increased VNet limits for Private Endpoints 3 Aprile 2025
