Notizie per Categorie
Articoli Recenti
- Explore practical best practices to secure your data with Microsoft Purview 25 Aprile 2025
- New whitepaper outlines the taxonomy of failure modes in AI agents 24 Aprile 2025
- Understanding the threat landscape for Kubernetes and containerized assets 23 Aprile 2025
- [Launched] Generally Available: Instance Mix for Virtual Machine Scale Sets 22 Aprile 2025
- Microsoft’s AI vision shines at MWC 2025 in Barcelona 22 Aprile 2025
- [Launched] Generally Available: Announcing the Next generation Azure Data Box Devices 22 Aprile 2025
- [Launched] Generally Available: Cross-Region Data Transfer Capability in Azure Data Box Devices 21 Aprile 2025
- [Launched] Generally Available: Azure Ultra Disk Storage is now available in Spain Central 21 Aprile 2025
- [Launched] Generally Available: Azure Firewall resource specific log tables get Azure Monitor Basic plan support 21 Aprile 2025
- Hannover Messe 2025: Microsoft puts industrial AI to work 21 Aprile 2025
Microsoft threat intelligence presented at CyberWarCon 2022
At CyberWarCon 2022, Microsoft and LinkedIn analysts presented several sessions detailing analysis across multiple sets of actors and related activity. This blog is intended to summarize the content of the research covered in these presentations and demonstrates Microsoft Threat Intelligence Center’s (MSTIC) ongoing efforts to track threat actors, protect customers from the associated threats, and share intelligence with the security community.
The CyberWarCon sessions summarized below include:
- “They are still berserk: Recent activities of BROMINE” – a lightning talk covering MSTIC’s analysis of BROMINE (aka Berserk Bear), recent observed activities, and potential changes in targeting and tactics.
- “The phantom menace: A tale of Chinese nation-state hackers” – a deep dive into several of the Chinese nation-state actor sets, their operational security patterns, and case studies on related tactics, techniques, and procedures (TTPs).
- “ZINC weaponizing open-source software” – a lighting talk on MSTIC and LinkedIn’s analysis of ZINC, a North Korea-based actor. This will be their first public joint presentation, demonstrating collaboration between MSTIC and LinkedIn’s threat intelligence teams.
MSTIC consistently tracks threat actor activity, including the groups discussed in this blog, and works across Microsoft Security products and services to build detections and improve customer protections. As with any observed nation-state actor activity, Microsoft has directly notified customers that have been targeted or compromised, providing them with the information they need to help secure their accounts. Microsoft uses DEV-#### designations as a temporary name given to an unknown, emerging, or a developing cluster of threat activity, allowing MSTIC to track it as a unique set of information until we reach a high confidence about the origin or identity of the actor behind the activity. Once it meets the criteria, a DEV is converted to a named actor.
They are still berserk: Recent activities of BROMINE
BROMINE overlaps with the threat group publicly tracked as Berserk Bear. In our talk, MSTIC provided insights into the actor’s recent activities observed by Microsoft. Some of the recent activities presented include:
- Targeting and compromise of dissidents, political opponents, Russian citizens, and foreign diplomats. These activities have spanned multiple methods and techniques, ranging from the use of a custom malicious capability to credential phishing leveraging consumer mail platforms. In some cases, MSTIC has identified the abuse of Azure free trial subscriptions and worked with the Azure team to quickly take action against the abuse.
- Continued targeting of organizations in the manufacturing and industrial technology space. These sectors have been continuous targets of the group for years and represent one of the most durable interests.
- An opportunistic campaign focused on exploiting datacenter infrastructure management interfaces, likely for the purpose of access to technical information of value.
- Targeting and compromise of diplomatic sector organizations focused on personnel assigned to Eastern Europe.
- Compromise of a Ukrainian nuclear safety organization previously referenced in our June 2022 Special Report on Defending Ukraine (https://aka.ms/ukrainespecialreport).
Overall, our findings continue to demonstrate that BROMINE is an elusive threat actor with a variety of potential objectives, yet sporadic insights from various organizations, including Microsoft, demonstrate there is almost certainly more to find. Additionally, our observations show that as a technology platform provider, threat intelligence enables Microsoft’s ability to protect both enterprises and consumers and disrupt threat activity affecting our customers.
The phantom menace: A tale of China-based nation state hackers
Over the past few years, MSTIC has observed a gradual evolution of the TTPs employed by China-based threat actors. At CyberWarCon 2022, Microsoft analysts presented their analysis of these trends in Chinese nation-state actor activity, covering:
- Information about new tactics that these threat actors have adopted to improve their operational security, as well as a deeper look into their techniques, such as leveraging vulnerable SOHO devices for obfuscating their operations.
- Three different case studies, including China-based DEV-0401 and nation-state threat actors GALLIUM and DEV-0062, walking through (a) the initial vector (compromise of public-facing application servers, with the actors showing rapid adoption of proofs of concept for vulnerabilities in an array of products), (b) how these threat actors maintained persistence on the victims (some groups dropping web shells, backdoors, or custom malware), and (c) the objectives of their operations: intelligence collection for espionage.
- A threat landscape overview of the top five industries that these actors have targeted—governments worldwide, non-government organizations (NGO)s and think tanks, communication infrastructure, information technology (IT), and financial services – displaying the global nature of China’s cyber operations in the span of one year.
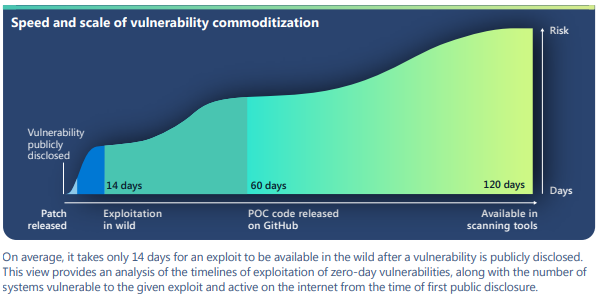
As demonstrated in the presentation, China-based threat actors have targeted entities nearly globally, employing techniques and using different methodologies to make attribution increasingly harder. Microsoft analysts assess that China’s cyber operations will continue to move along their geopolitical agenda, likely continuing to use some of the techniques mentioned in the presentation to conduct their intelligence collection. The graphic below illustrates how quickly we observe China-based threat actors and others exploiting zero-day vulnerabilities and then those exploits becoming broadly available in the wild.
ZINC weaponizing open-source software
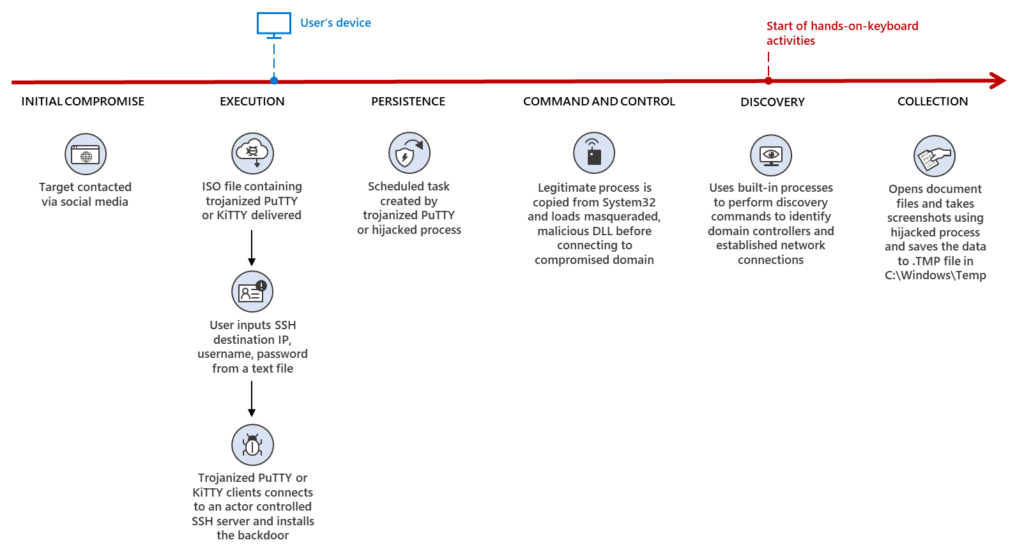
In this talk, Microsoft and LinkedIn analysts detail recent activity of a North-Korea based nation-state threat actor we track as ZINC. Analysts detailed the findings of their investigation (previously covered in this blog) and walked through the series of observed ZINC attacks that targeted 125 different victims spanning 34 countries, noting the attacks appear to be motivated by traditional cyber-espionage and theft of personal and corporate data. A few highlights include:
- In September 2022, Microsoft disclosed detection of a wide range of social engineering campaigns using weaponized legitimate open-source software. MSTIC observed activity targeting employees in organizations across multiple industries including media, defense and aerospace, and IT services in the US, UK, India, and Russia.
- Based on the observed tradecraft, infrastructure, tooling, and account affiliations, MSTIC attributes this campaign with high confidence to ZINC, a state-sponsored group based out of North Korea with objectives focused on espionage, data theft, financial gain, and network destruction.
- When analyzing the data from an industry sector perspective, we observed that ZINC chose to deliver malware most likely to succeed in a specific environment, for example, targeting IT service providers with terminal tools and targeting media and defense companies with fake job offers to be loaded into weaponized PDF readers.
- ZINC has successfully compromised numerous organizations since June 2022, when the actor began employing traditional social engineering tactics by initially connecting with individuals on LinkedIn to establish a level of trust with their targets.
- Upon successful connection, ZINC encouraged continued communication over WhatsApp, which acted as the means of delivery for their malicious payloads. MSTIC observed ZINC weaponizing a wide range of open-source software including PuTTY, KiTTY, TightVNC, Sumatra PDF Reader, and muPDF/Subliminal Recording software installer for these attacks. ZINC was observed attempting to move laterally across victim networks and exfiltrate collected information from.
As the threat landscape continues to evolve, Microsoft strives to continuously improve security for all, through collaboration with customers and partners and by sharing our research with the larger security community. We would like to extend our thanks to CyberWarCon and LinkedIn for their community partnership.
The post Microsoft threat intelligence presented at CyberWarCon 2022 appeared first on Microsoft Security Blog.
Source: Microsoft Security
