Notizie per Categorie
Articoli Recenti
- Explore practical best practices to secure your data with Microsoft Purview 25 Aprile 2025
- New whitepaper outlines the taxonomy of failure modes in AI agents 24 Aprile 2025
- Understanding the threat landscape for Kubernetes and containerized assets 23 Aprile 2025
- [Launched] Generally Available: Instance Mix for Virtual Machine Scale Sets 22 Aprile 2025
- Microsoft’s AI vision shines at MWC 2025 in Barcelona 22 Aprile 2025
- [Launched] Generally Available: Announcing the Next generation Azure Data Box Devices 22 Aprile 2025
- [Launched] Generally Available: Cross-Region Data Transfer Capability in Azure Data Box Devices 21 Aprile 2025
- [Launched] Generally Available: Azure Ultra Disk Storage is now available in Spain Central 21 Aprile 2025
- [Launched] Generally Available: Azure Firewall resource specific log tables get Azure Monitor Basic plan support 21 Aprile 2025
- Hannover Messe 2025: Microsoft puts industrial AI to work 21 Aprile 2025
Microsoft Security tips for mitigating risk in mergers and acquisitions
Sixty-two percent of organizations that undertake mergers and acquisitions face significant cybersecurity risks or consider cyber risks their biggest concern post-acquisition.1 Threat actors that focus on corporate espionage often target the acquiring company, which we will refer to as the Parent, early in the bidding process to gain a competitive advantage. Other threat actors focus on planting backdoors in the entity being acquired, which we will refer to as the Acquisition with the intent of later compromising the Parent company.
A Parent company can take several approaches to integrating the Acquisition within the organization’s IT environment. These include migrating the Acquisition’s services and users into the Parent’s IT environment or directly connecting the Acquisition’s IT environment through technical means. (See Figure 1.)
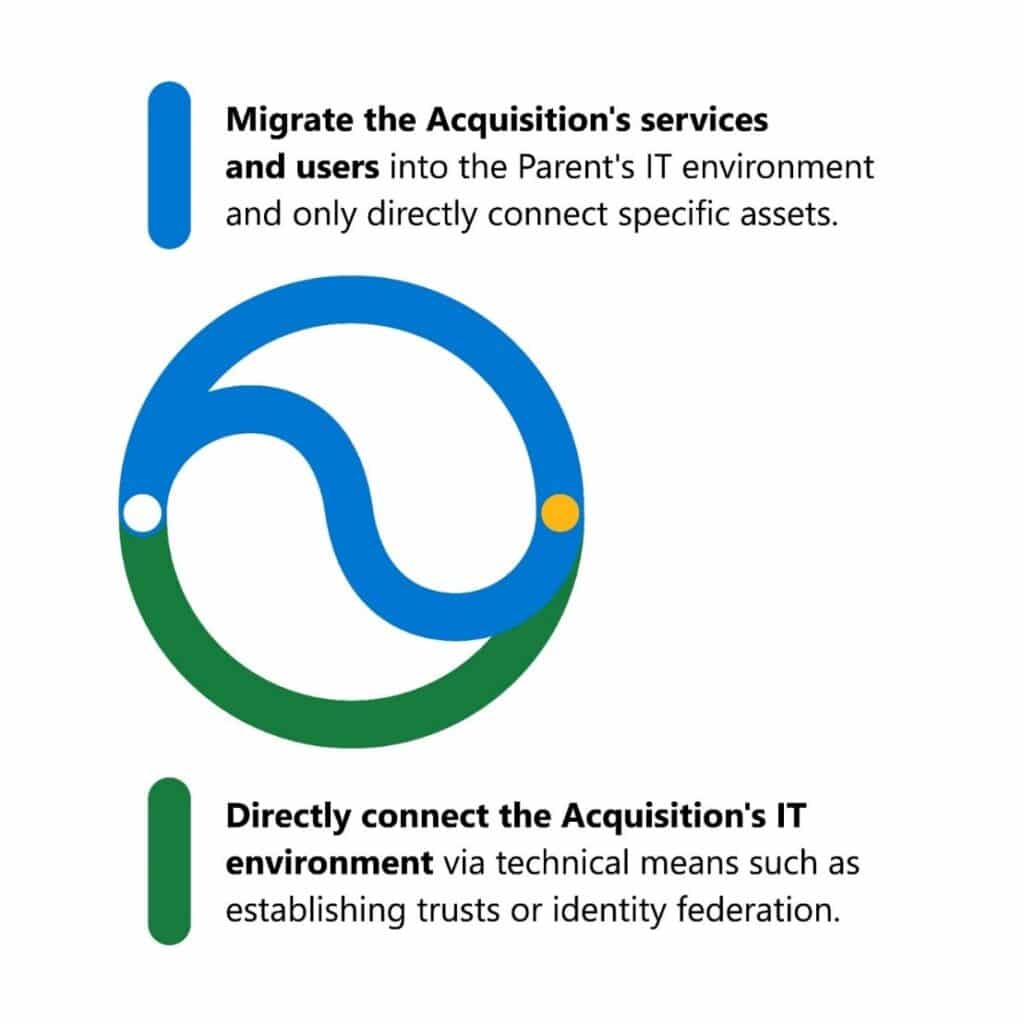
Figure 1. Two avenues IT leadership can take with mergers and acquisitions.
The first option has long-term security benefits, given that only selected elements of the Acquisition are incorporated into the Parent environment. On the other hand, depending on the complexity of both parties, this process can be time-consuming and costly.
The second option can be quicker to execute and reduce disruption to the operations of both parties; however, there may be hidden security and technical debt that may be costly to address in the long term.
So, what should an organization consider when determining the best plan of action for security in a merger or acquisition?
Security risks in mergers and acquisitions
It is common for a Parent to make the decision based solely on economic considerations driven by the costs of time and effort; however, there are significant cybersecurity considerations that should be factored into the decision-making process to ensure the long-term security of both the Parent and the Acquisition.
These include:
- Technical debt: Understand how much technical debt you will inherit. Every organization carries some technical debt, and the key in mergers and acquisitions is transparency. It is critical for a Parent to understand the technical debt it will be inheriting to understand how it will compound the Parent’s own technical debt and assist in quantifying any remediation costs.
- Existing security (not exclusive to cybersecurity): Consider how the two parties will consolidate key security capabilities, such as endpoint detection and response (EDR) tools or antivirus. Also consider how they both coordinate Security teams, such as security operations and security engineering, to avoid carrying numerous capabilities, tools, and data sources.
- Compliance and regulatory implications: Research how the Acquisition handles personally identifiable information (PII), like bank account numbers, and know the regulations it must abide by, its compliance procedures, and compliance history, including any regulatory violations. If the Acquisition is in a different country or region with stricter data privacy regulations, for instance, those are the ones both Parent and Acquisition should follow in relation to shared data.
- Misconfiguration and misutilization of existing systems: Review the configuration of systems at the Acquisition because they may have been set up incorrectly, perhaps due to complexity or a lack of accountability, or they may be insufficiently utilized because of incomplete deployment, or no one has the skills to use it. You may find that the misconfiguration slipped through because there’s no testing of new systems before they are introduced. That’s a serious issue because security misconfigurations become the Parent’s liabilities.
- Identity: Enable multifactor authentication (MFA) flow and other identity controls. Security teams should review the identity configuration, which may be bypassed because it wasn’t architected in a way that works for both companies.
- Network: Evaluate how to connect legacy devices. In a merger or acquisition, it may not be possible to connect legacy devices with each other (for example, if a customer has devices that are not considered next-generation firewalls). With older firewalls, you lose the ability to apply security controls and logging isn’t as enhanced.
- Cloud: Check whether Microsoft Azure subscriptions have MFA enabled, ports that are open in Azure infrastructure as a service, and the controls for federated identities with other providers. Conditional Access policies may cancel each other out.
- Password Management: Consider who has more access—the threat actor or you? To help ensure it’s you, secure access to your data using Privileged Identity Management and Privileged Access Management tools.
- New threats: Anticipate new threats and new-to-you threats. A small manufacturer, for example, may not know of a large-scale security threat but once acquired by a global corporation, it could become a target. Threat actors may see an acquisition as an opportunity to access the Parent through the Acquisition.
The two most common avenues of risk are:
- Current actor persistence in the acquired environment: The actor’s already there and you’re giving them an opportunity to enter the Parent environment when you connect them. This is the most obvious and ideal path.
- The security architecture of the acquired environment: It’s too hard to go against the Parent environment directly because its security posture is simply too costly for an attacker to go after, given what they could potentially gain in value. Instead, a threat actor targets the Acquisition.
If a threat actor knows about a pending acquisition, they can do reconnaissance on the acquired company to see if its security posture is weaker than the Parent’s. It may be a more attractive target to gain access to the Parent through the weaker acquisition environment.
The Acquisition likely receives support from multiple service providers. If any of those service providers are compromised, a threat actor could move into the Acquisition’s environment and then gain access to the Parent. Carefully consider the connections you have with vendors because they could bring a potentially unknown compromise and introduce security vulnerabilities and architectural weaknesses.
Deeper due diligence is key
The due diligence processes each company undergoes when making an investment will vary depending on the company, industry, and region. While there is no universal standard, it is critical that companies get it right and understand potential areas of concern they may be inheriting.
Ultimately, your organization is acquiring whatever unknowns are present in that environment. So that’s why it is important to ask questions before, during, and after a merger and acquisition. Anything persistent and any open backdoors affecting your environment provide a direct path into the Parent organization.
Security questions to ask before a merger or acquisition
Both parties need to foster open and honest communication and share technical data. Commit to transparency. From the exploratory phase to the official merger and acquisition negotiation process, both parties should understand the expectations, so they don’t miss details during the merger or acquisition.
Mergers and acquisitions are dynamic and complex. To achieve the economic goals of mergers and acquisitions, business leaders must understand the attack surface they’re onboarding. Discovering and cataloging the partner company’s resources and digital assets, from within the corporate perimeter to the entire internet, is a critical step of any due diligence process. These include known and unknown assets, including resources developed outside the purview of security and IT teams, like shadow IT. These audits can’t be outsourced or done just for compliance. They are top priorities every executive needs to consider to future-proof their investments.
The first step is to establish a baseline set of known facts. Ask these questions during your initial discovery phase and as part of a proactive assessment:
- What is your basic security structure?
- What is your antivirus and is it up to date?
- What is your EDR solution?
- How are you managing identity protection?
- How are you managing data access protection?
- Does the acquired company meet the current security standards of the Parent?
- How are security issues triaged?
- Do you have a form of central logging (security information and event management; security orchestration, automation, and response) solution?
- How are you tracking and repairing your online vulnerabilities and compliance risks (unmanaged assets or those that have been forgotten)?
As you get deeper into the due diligence phases, ask these questions to understand their compromise history:
- What is your history of security compromise?
- When did these compromise(s) occur?
- What are the details?
- What are the root causes of those security compromises?
- How were the threats mitigated?
- Do you have a post-incident review process? What were the results?
After this disclosure, the most important question to ask is, “Did you remediate it?” If the Acquisition had a ransomware attack or other cyberattack, what happened? If the Acquisition had an unpatched vulnerability and was able to privilege-escalate to domain admin and deploy the ransomware, we ask, what is your patching?
Before setting up legal frameworks, disclose past events and understand how to remediate what caused them. Ignore this recommendation to avoid fireworks of the non-celebratory kind.
Security questions to ask after a merger or acquisition
Arguably, the greatest risk to mergers and acquisitions security is establishing trust relationships or merging hundreds or thousands of systems into the Parent company’s enterprise infrastructure. The health and configuration of those systems should be evaluated for security risks. The presence of any malware or advanced persistent threat (APT) backdoors in the subsidiary company can threaten the Parent company after the merger. Security misconfigurations and risky decisions become the Parent company’s liabilities. Also, threat profiles need to be re-evaluated to include any geopolitical changes caused by the mergers and acquisitions process. For example, a small parts manufacturer would not be expected to be aware of risks from larger known threat actors (such as Phineas Phisher2), but after being acquired by a global oil company, it would need to be.
Take the information gathered during the pre-merger question and answer session, including compromise exposures and an analysis of the Acquisition’s existing security posture against a reference standard, and decide how to integrate that environment into yours, along with detailing the necessary technical steps. To integrate the acquired company into your environment, you’ll need to bring its security posture to your level. The Parent company will have to implement basic security practices. Here are steps to evaluate and prioritize:
- Assess existing systems that will be part of the acquisition and the risks associated.
- Conduct remediation based on those results.
- Understand the timeline for integrating the networks and know whether the data is located on-premises or in the cloud.
- Learn the process for asset refresh and retirement of systems.
- Conduct a penetration test or risk assessment and evaluate security policies and security gaps.
What actions should companies take?
The Microsoft Detection and Response Team (DART) has worked on incident response cases where companies were breached within an hour of completing a post-merger integration. In these cases, the threat actor’s subsidiary backdoor was granted two-way trust access to the Parent company’s Microsoft Azure Active Directory (Azure AD), third-party identity providers with any form of federation, and on-premise Active Directory forest.
DART has also had to explain to customers the probable connection between an APT actor’s backdoor uncovered in its environment, and the fact that its new Parent company’s bid was the lowest amount—to the dollar—that they were willing to accept during an acquisition. For these reasons and others, many of DART’s customers ask for security assessments before, during, or immediately after completing mergers and acquisitions.
Take these steps:
- Set the expectations of disclosure and the level of information shared about security issues early in the talks. Make this a standard part of the exploratory process when setting up the legal framework of how the merger and acquisition will run.
- Do a pre-mergers and acquisitions security assessment, whether a proactive threat hunt that includes cross-platform systems (Mac and Linux) and third-party identity providers, or an Azure AD security assessment, or an evaluation of the maturity of the environment’s security posture.
- Focus on evaluating and improving security visibility and logging early in the mergers and acquisitions process. This allows first-party and third-party security teams to assess and react to security issues promptly. For mergers and acquisitions-related threats, focus first on securing identity, access control, and communications.
- Focus security and risk audits on cataloging the company’s resources and digital assets, including the company’s external attack surface, or catalog of internet-facing assets that an attacker could leverage to gain a foothold for an attack. External attack surface management (EASM) products can highlight a range of hygiene issues, corresponding indicators of compromise and vulnerabilities, and compliance issues, giving mergers and acquisitions teams the baseline they need to conduct a cyber risk assessment and drive post-mergers and acquisitions program.
Cybersecurity risk in mergers and acquisitions is an increasing issue for both IT security and business decision-makers. Giving the IT security teams sufficient time to do thorough assessments, due diligence, inventories, and putting more controls in place will determine how much of that risk can be mitigated.
Learn more
To learn more about Microsoft Security solutions, visit our website. Bookmark the Security blog to keep up with our expert coverage on security matters. Also, follow us at @MSFTSecurity for the latest news and updates on cybersecurity.
1The Role of Cybersecurity in Mergers and Acquisitions Diligence, Forescout. 2019.
2Hacker who hacked Hacking Team published DIY how-to guide, Ms. Smith, CSO. April 17, 2016.
The post Microsoft Security tips for mitigating risk in mergers and acquisitions appeared first on Microsoft Security Blog.
Source: Microsoft Security
